Oftentimes, cyber attackers are able to infiltrate the networks of organizations through holes in older programs which have not been updated.
Recently, a malware known as “DoublePulsar” has been found targeting un-patched Windows systems, inserting itself within networks and laying seeds for future ransomware attacks.
Here’s what’s currently known about this threat and what steps you can take to prevent yourself from falling victim to it.
An Advanced Attacker
As reported in Bank Info Security, a group of hackers known as the “Shadow Brokers” – believed to have ties with the Russian government – released a set of attack tools which exploit flaws in older versions of Windows.
One of these tools, DoublePulsar, has been adopted by attackers and implanted in thousands of servers, security researcher Kevin Beaumont noted on Twitter. While DoublePulsar may not currently pose an active threat to your organization, it is keeping the door open for hackers to come in and steal or encrypt your files.
DoublePulsar and other similar malware were originally designed by the “Equation Group,” a highly advanced threat actor with suspected ties to the United States National Security Agency. What this means for you is that this attacker is very sophisticated, and you need to either take steps to update your Windows devices or remediate your already compromised network immediately.
The Fix
The simplest way to protect yourself from attacks like this is to regularly download Microsoft patches and actually install them. The patch itself will do nothing unless you take action to implement it into your network.
Furthermore, older Windows versions including Server 2003, XP and Vista are no longer supported, meaning if you are still using these versions, you will not receive any updates at all. Obviously, this will leave you open to a wide range of attacks far beyond the threat DoublePulsar presents. Even one computer in your organization using outdated software like this is a threat to your network.
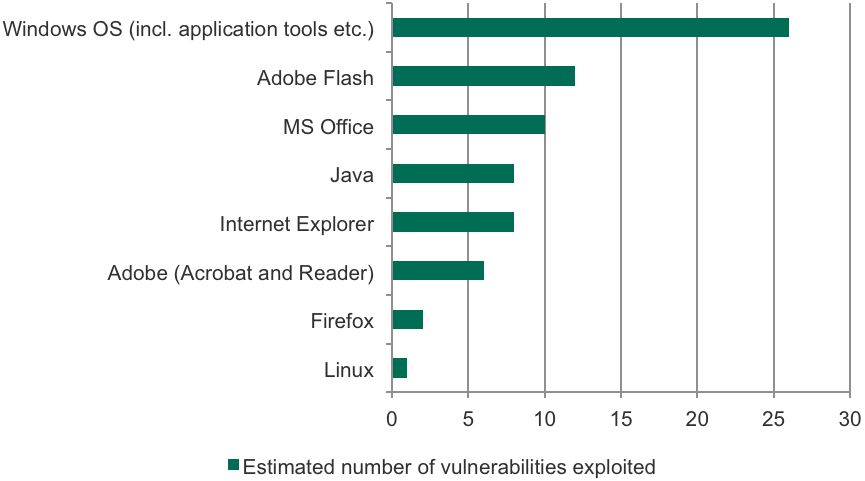
This is a habit you need to get yourself into. Kaspersky Labs recently released a report that detailed which system flaws were most often targeted by attackers. As the image below shows, Windows is far ahead the leader in this category.
If you have a PC-dominant work environment, then take stock of which Windows operating systems are used throughout your organization. Work with your IT provider to update all devices, and institute a companywide policy on installing Windows updates as they are released.
If you suspect your network might be compromised, our Compromise Assessment helps an organization find malicious code through deployment of highly-specialized, yet nonintrusive, forensic software on all endpoints. Our detection capabilities include: identification of attacks from stealth/idle malware, zero-day code, rootkits, Trojans, key loggers and various forms of data capturing programs. Anything that appears suspicious is carefully examined to confirm its validity in your environment.
If you suspect any attacker has breached your network, contact us today,